This post deals with the Cloudflare service (CF website link). What is it, how it works and how to protect a website using their services.
Note:
See my forum’s discussion thread about “Cloudflare being shady” – and consider that before deciding whether to go with Cloudflare.
Contents:
- What is Cloudflare?
- How does it work?
- Services offered
- How to setup Cloudflare with a WordPress website
- My experience
- My opinion and a note
- Cloudflare video demonstration
1. What is Cloudflare?
Basically, it’s a service that can be “placed between” a website’s hosting server and visitors. It can serve multiple purposes: DNS, CDN (reverse proxy) and DDoS attack (Wiki link) protection.
There are various service levels: from completely free, to “enterprise” that goes over several hundred US dollars per month. The free package is quite functional for most small, medium and even some large websites. Cloudflare’s policy is to get people to test the service for free (and use them as test subjects for the service at the same time), knowing they will later be willing to pay for more of what they like.
An example of this pricing policy: in the post about redirections, I explained how they can be set up using Cloudflare Page Rules. Free service gives you 3 Page Rules, while each additional 5 cost 5$ per month.
If you read this phishing attack attempt incident report at Cloudflare (Cloudflare website link), you’ll understand why I believe Cloudflare’s security is way above average.
2. How does it work?
There’s a vast network of Cloudflare servers across the whole planet. The traffic of websites that use these services is usually routed to the server closest to the website visitor first.

Source: Cloudflare
Picture 1
Servers contain a copy of website static data, while dynamic (and non-cacheable) data is updated from the website host server, using the fastest available network infrastructure (more expensive plans offer “Railgun” – technology Cloudflare developed with some ISP-s to provide fast data transfer).
In order for this to work and all the traffic to first go through Cloudflare servers, website owner must set up the domain to use Cloudflare’s DNS. With this set up, in addition to providing a fast and good quality DNS, Cloudflare will also protect the website from attacks, practically hiding the host server behind its network.
3. Services offered
There are four price levels, with services of each level including all the previous level services, plus services of that level. Without going into details, more expensive plans offer better DDoS and Firewall protection, better caching, more customization and faster technical support answers. More details on packages and prices can be found on Cloudflare’s website.
The Free package is quite good and webmasters can usually tell when they need something more. It will offer you:
- More speed – through better routing, and a (rudimentary in the free package) CDN service.
- More security – acting as a firewall between your hosting server and the “outer world,” plus it hides your server’s IP address.
- Easier website maintenance – Cloudflare’s DNS changes propagate super-fast. Unlike the “normal” DNS changes that take up to 24 hours to propagate, Cloudflare gets it done within minutes.
4. How to setup Cloudflare with a WordPress website
These instructions are for those using SSL (many hosting providers offer free SSL with Let’s Encrypt), which is advisory. All the options not mentioned should be left as they are (by “default”).
Make an account on Cloudflare.com and click the button: “+ Add a Site”. Then, after entering the domain name, you will be given a list of two nameservers – which should be entered instead of the existing nameservers on your domain registrar. Depending on the registrar you use, the menu might differ from picture 2:

Picture 2
A separate post explains how to set up nameservers.
Of course, you should configure Cloudflare’ DNS (a separate article explaining how to do that).
The rest of this chapter is obsolete. Cloudflare has changed its menus and options since I wrote this, so I wrote a new article explaining how to configure Cloudflare for a WordPress website.
You can just skip to chapter 5 to read about my experience and my final note (of caution).
Make a page rule to not cache the website when administrating it (of course, replace “example.com” part with your website domain):
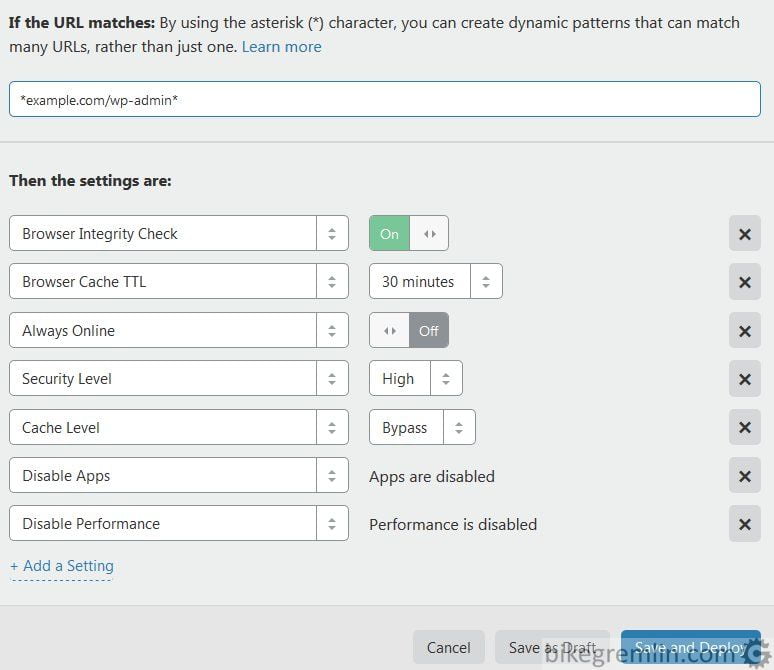
Picture 3
These two rules ensure that no one can visit the website without encryption and that while administrating the website, no cached content is shown to the administrator. After that, one can setup other options from Cloudflare menu, one by one. Here’s how I did it on my website(s):
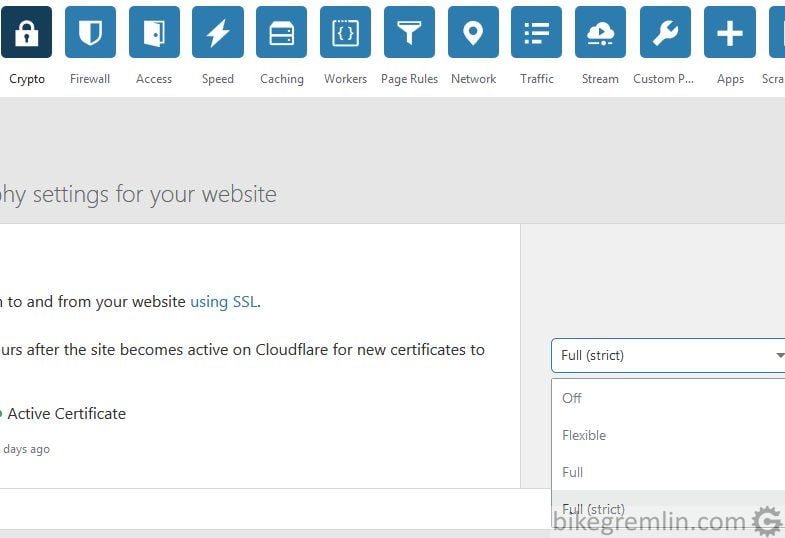
Picture 4
In the Crypto menu, if the website has an SSL certificate, it will usually work with “Full (strict)” option enabled. If there is no widely (and by Cloudflare) recognized SSL certificate, then “Full” option will work, while “Flexible” is for servers without certificates (when the communication between Cloudflare and the hosting server will not be encrypted). More details on Cloudflare support.
Other options that should be setup here are (without explaining why):
- Always Use HTTPS: On
- Authenticated Origin Pulls: Off – if server is not set up for it and/or if using RailGun – info.
- Minimum TLS Version: TLS 1.2
- Opportunistic Encryption: On
- Onion Routing: On
- TLS 1.3: Enabled+0RTT
- Enable Universal SSL (unless Cloudflare Dedicated SSL is bought)
Firewall menu, again, briefly:
- Security Level: Medium
- Challenge Passage: 1 day
- Privacy Pass Support: On
Speed menu:
- Auto Minify: select all
- Enable Accelerated Mobile Links: On
- Brotli: On
- Rocket Loader™: On
Caching menu:
- Caching Level: Standard
- Browser Cache Expiration: Respect Existing Headers (if website caching is set up)
- Always Online™: On
Scrape Shield menu:
- Hotlink protection: On
In a separate post, I explained how to set up Cloudflare DNS.
5. My experience
Bikegremlin.com uses Cloudflare since the summer of 2018. So far so good (my Cloudflare configuration). I do see slightly better page load times and lower server load when Cloudflare is used. I haven’t had any serious attacks, though I suppose an additional security layer isn’t a bad thing (update: yes, it does help with the attacks). Pictures 5 and 6 show a few stats from last month:
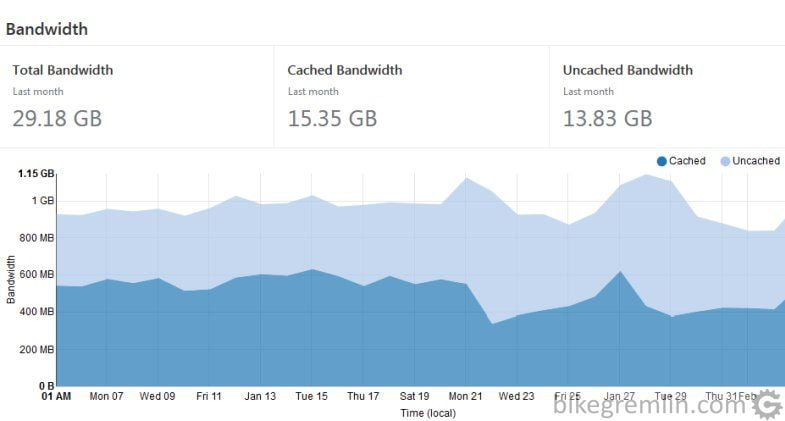
Picture 5
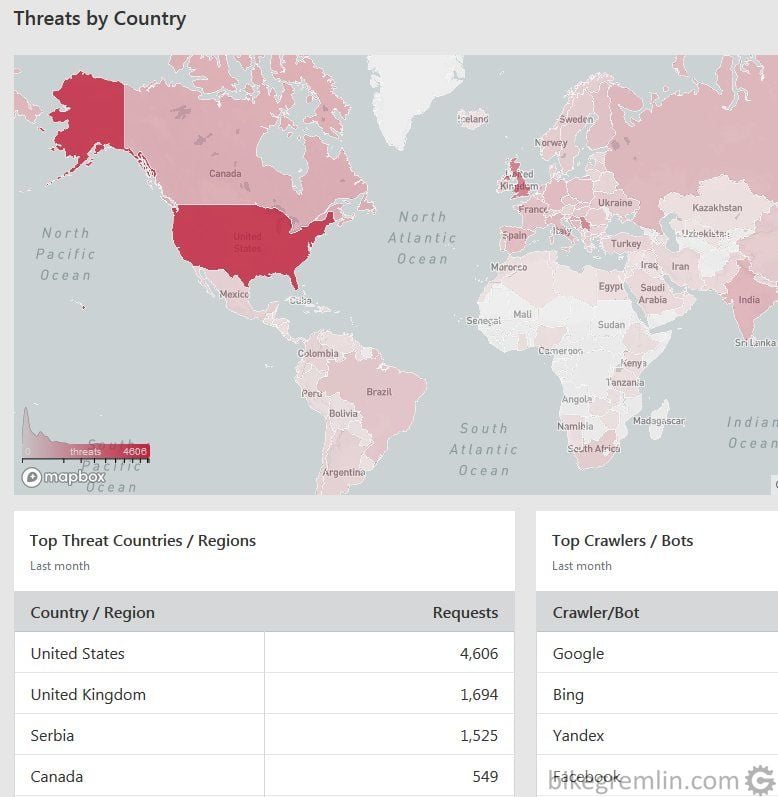
Picture 6
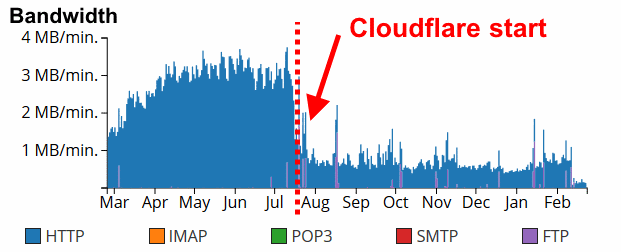
Picture 7
6. My opinion and a note
Take the information in this chapter as my personal opinion, ie: “to the best of my knowledge”, or “as far as I know”.
Important: related to any data encrypted using SSL/TLS encryption (HTTPS protocol) on the way to and from your hosting server. All that data gets decrypted on Cloudflare proxy servers (unless you use “grey could,” when Cloudflare acts as an ordinary DNS). They are then re-encrypted on the way to and from the website visitors. Otherwise caching and protection wouldn’t work. This means that Cloudflare (owners) can read all the data. They can record it, sell it, show it to anyone. They can even alter it if they wish, working as a man-in-the-middle attacker.
Does Cloudflare do this? They swear they don’t. It would certainly harm their reputation. Also, their business model is based on up-sales of extra services, so I don’t think they need to sell customer data (unlike some other large corporations). Still, I think it’s only fair for me to let you know that, technically, they could do that. Like Google, Cloudflare is a big brother that (for now) smiles gently and offers us a lot of great stuff for free. I’m using it, though my websites are set up so that they could easily work without it.
I wrote in a bit more detail about how this all works, and how it is configured in the article about Cloudflare DNS setup.
Update: I also wrote a new article explaining how to configure Cloudflare for a WordPress website?
7. Cloudflare video demonstration
How to open and secure a Cloudflare account, how to configure nameservers to have your website run using Cloudflare, speed, secrurity and privacy (GDPR):